Has GSA Adopted DoD’s CMMC Requirements?
If you hold or pursue GSA contracts, pay attention. The General Services Administration (GSA) just raised the bar on cybersecurity compliance, and unlike DoD’s phased CMMC rollout, these requirements are effective immediately.
On January 5, 2026, GSA published a new IT Security Procedural Guide for protecting Controlled Unclassified Information (CUI). The guide slipped out without a press release or industry comment period, but make no mistake—this is the direction GSA is heading.
Here’s what you need to know.
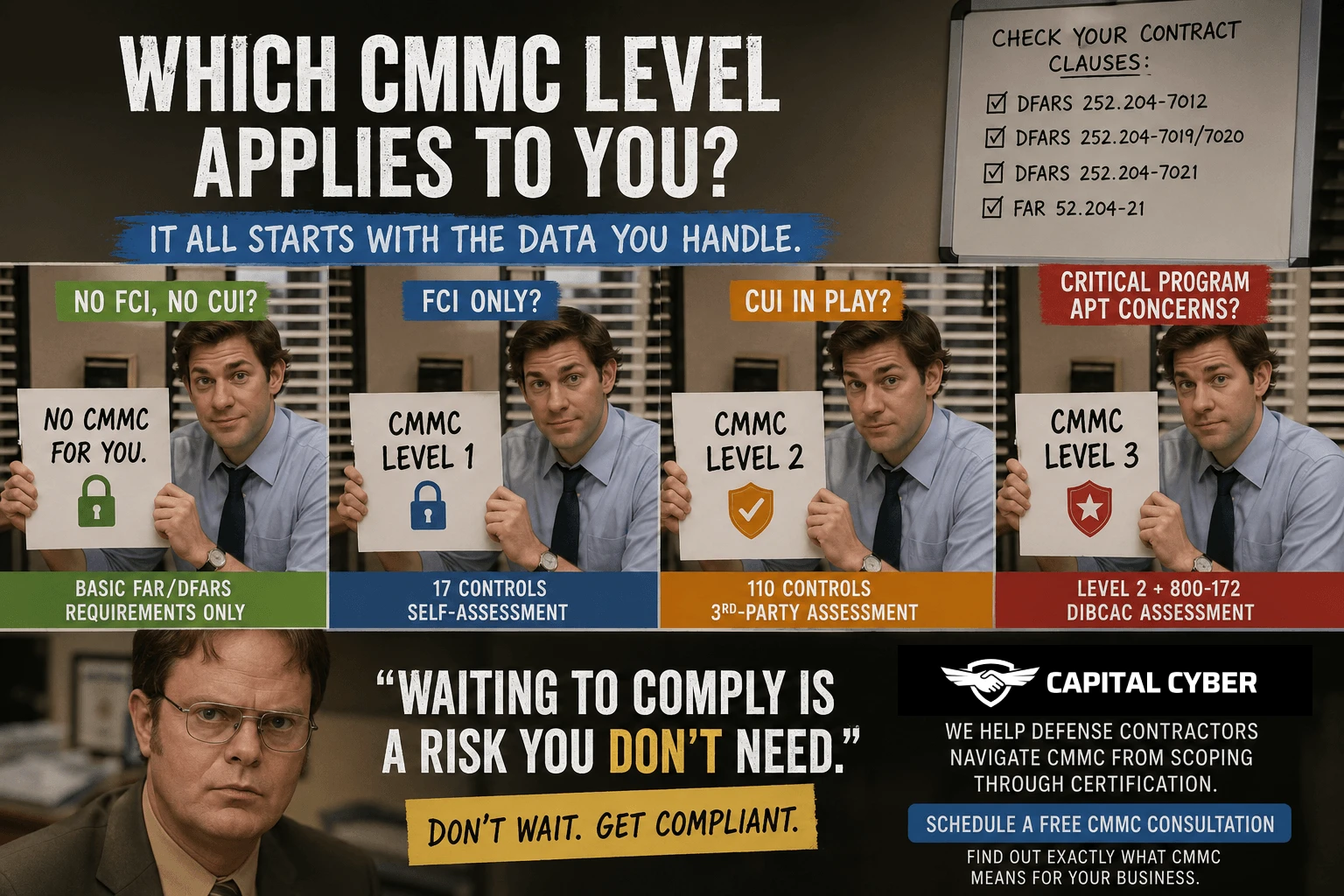
What’s Different From DoD’s CMMC?
DoD’s CMMC program focuses on defense contractors handling CUI and Federal Contract Information (FCI). GSA’s new guide takes a broader approach.
While CMMC is rolling out in phases over four years, GSA isn’t waiting. Their framework applies to all contractors working with CUI across any GSA contract vehicle—including the governmentwide Multiple Award Schedule (MAS).
Key differences:
- No transition period. GSA’s requirements are effective now.
- “Showstopper” controls. GSA will approve systems that meet certain critical controls while requiring a Plan of Actions and Milestones (POA&M) for everything else.
- One-hour incident reporting. Not 72 hours like CMMC. One hour.
The practical impact: if you do business with GSA, you likely fall under these requirements whether you’ve heard about them or not.
The Five-Phase CUI Framework
GSA’s guide mirrors NIST’s Risk Management Framework. Here’s the breakdown:
Phase 1: Prepare
Figure out what types of information your systems process, store, or transmit. Use FIPS 199 security categorization to categorize your data. Then submit your solution architecture and security capabilities to GSA for review.
You’ll work with GSA’s Information System Security Officer (ISSO) and Chief Information Security Officer (CISO) throughout this process.
Phase 2: Document
Prepare and submit several key documents:
- System Security and Privacy Plan (SSPP)
- Privacy Threshold Assessment (PTA)
- Privacy Impact Assessment (PIA)
- Architecture Review Checklist
- Supply Chain Risk Management Plan
Fair warning: documentation built for other programs like CMMC or FedRAMP generally won’t satisfy GSA’s requirements. Each agency has its own criteria.
Phase 3: Assess
Engage a third-party assessor—either a FedRAMP Third Party Assessment Organization (3PAO) or GSA-approved independent assessor—to test your systems. This assessment must be agreed upon in advance by GSA.
Phase 4: Authorize
GSA conducts a multi-level review of your approval package. They prepare a Memorandum for Record evaluating whether your systems are sufficiently secure to handle CUI.
Phase 5: Monitor
Once approved, you’re not done. You must:
- Submit quarterly vulnerability scanning reports
- Update your POA&M quarterly
- Provide annual SSPPs, PTAs, and PIAs
- Undergo third-party assessment every three years
- Immediately report any major system changes to GSA
The One-Hour Incident Reporting Rule
This is the requirement that should grab your attention.
If you discover a CUI incident—whether suspected or confirmed—you have one hour to report it.
Compare that to:
- CMMC’s 72-hour window
- FAR CUI proposed rule’s 8-hour window
- GSA’s one-hour window
The Guide doesn’t define what ‘escalation’ means for missing this deadline, but you can assume it won’t be good.
Practical concern: one hour barely allows time to confirm an incident happened, let alone conduct a meaningful investigation. Expect to file incomplete initial reports and follow up with additional details. Build your incident response processes with this tight window in mind.
What About NIST SP 800-171 Rev. 3?
Here’s something that trips up even experienced contractors.
GSA’s guide requires Revision 3 of NIST SP 800-171. DoD’s CMMC program currently requires Revision 2.
Revision 3 reorganizes and consolidates several of the 110 security controls. It places greater emphasis on:
- Supply chain risk management
- Continuous monitoring
- Stronger authentication requirements
If you’re already CMMC compliant under Rev. 2, you’re not automatically compliant under GSA’s requirements. The frameworks overlap but aren’t identical. Review the differences carefully.
The ‘Showstopper’ Controls
GSA identified five critical controls that must be implemented before they’ll approve your system:
- Multi-factor authentication
- Vulnerability monitoring and scanning
- Secure remote access controls
- Cryptographic protection
- Replacement of unsupported components
Meet these five, and GSA will conditionally approve your system even if other controls are lacking. You’ll still need a POA&M for the gaps, but you won’t be blocked from contract eligibility.
Think of these as your minimum viable security posture for GSA work.
What This Means for Subcontractors
The Guide is silent on subcontractor flow-down requirements. But the broader trend in CUI protection suggests primes should ensure subcontractors follow similar safeguards—even without express language requiring it.
If you’re a subcontractor in the GSA supply chain, expect your prime customers to start asking about your CUI controls. Better to get ahead of this now than scramble later.
What You Should Do Right Now
If you hold or pursue GSA contracts:
- Assess your CUI infrastructure against NIST SP 800-171 Rev. 3 and select controls from NIST SP 800-172 Rev. 3
- Start with the five ‘showstopper’ controls if nothing else—these unlock conditional approval
- Get in queue for a third-party assessment. The pool of qualified assessors is limited, and demand is about to spike
- Build incident response processes that can identify and report incidents within one hour
- Review your subcontractor relationships and ensure they follow CUI safeguarding best practices
The Capital Cyber Advantage
Capital Cyber helps GSA contractors navigate these requirements without the chaos.
We’ve worked with organizations across manufacturing, aerospace, engineering, and professional services to achieve CMMC certification and broader CUI compliance. We know the landscape, we know the assessors, and we know what GSA is looking for.
Schedule a Meeting with Rick
Rick leads our federal contractor compliance practice. He can assess your current situation, identify gaps, and outline exactly what it will take to meet GSA's new requirements.
- +1 (571) 410 3066
- info@capital-cyber.com
Capital Cyber | 1019B Edwards Ferry Rd. #1183, Leesburg, VA 20176.

Leave feedback about this