Not ready for a Complete Pen Test? How about finding out your Cyber Score in 2 mins? Click here for your Cyber Score
Published by Capital Cyber | Leesburg, VA | (571) 410 3066
If you are a defense manufacturer and your contracts touch Controlled Unclassified Information (CUI), CMMC Level 2 is the line you have to cross. There is no “Level 1.5.” There is no delay. And as of November 10, 2026, third-party Level 2 certification becomes the default requirement for most contracts involving CUI.
This is the complete 2026 guide to CMMC Level 2 requirements for defense manufacturers — what the 110 controls actually require, how the scoring works, which controls cannot be on a POA&M, and the real timeline to certification for CNC shops, aerospace suppliers, electronics manufacturers, and metal fabricators.
If you run a shop that supplies the DoD, read this carefully. The rules have teeth.
CMMC Level 2 — the Advanced tier of the Cybersecurity Maturity Model Certification — is built on 110 security requirements from NIST SP 800-171 Rev. 2, organized across 14 control families and measured by 320 distinct assessment objectives.
In plain English: if your manufacturing environment stores, processes, or transmits CUI — engineering drawings, technical data packages, specifications, ITAR-controlled data, or anything a prime contractor flows down under DFARS 252.204-7012 — Level 2 is the baseline that keeps you eligible for DoD contracts.
The DoD estimates roughly 80,000 contractors in the Defense Industrial Base need Level 2 certification. Most defense manufacturers are in that number.
Level 2 comes in two flavors, and knowing which one applies to you is step one.
Level 2 (Self-Assessment) — allowed for a narrow set of contracts involving CUI that is not critical to national security. You assess your own environment and submit results to the Supplier Performance Risk System (SPRS).
Level 2 (C3PAO Certification) — the default for most CUI contracts. An accredited Certified Third-Party Assessment Organization (C3PAO) conducts an independent audit of your implementation of all 110 controls.
Here is the reality for 2026: assume you need C3PAO certification unless the solicitation specifically says otherwise. The technical requirements are identical either way — only the verification method differs.
CMMC Level 2 organizes all 110 requirements across 14 NIST 800-171 control families. For defense manufacturers, here is what each one actually means on the shop floor:
The largest family. Covers who can access what. Includes MFA for privileged and non-privileged accounts, least-privilege enforcement, remote access controls, wireless and mobile device restrictions, and control over CUI flow. For manufacturers, this is usually the biggest lift — especially controlling access to CAD files, engineering drives, and CNC programming workstations.
Security awareness training for all users, insider threat awareness, and role-specific training for users with security responsibilities. Generic “phishing video once a year” does not satisfy this.
Immutable, time-stamped audit logs for everything touching CUI. Log review processes. Protection of audit information from unauthorized modification. This is where most manufacturers have the biggest gap — shop-floor systems often have no central logging at all.
Baseline configurations, change control processes, least-functionality hardening, software inventories, and restrictions on user-installed software. Your ERP, CAM system, and quoting tools all need documented baselines.
User identification, MFA enforcement, password complexity and reuse rules, cryptographic protection of authenticators. MFA is a gate control — not optional, not deferrable.
Documented incident response plan, user training on reporting, and the ability to track and respond to incidents. You also have to report cyber incidents to DoD within 72 hours under DFARS 252.204-7012.
Controlled and monitored maintenance activities, sanitization of systems removed for off-site maintenance, supervision of maintenance personnel without clearance. This one catches manufacturers off guard when third-party CNC technicians touch CUI-adjacent systems.
Protection of media containing CUI, sanitization before disposal or reuse, marking of CUI, limited media transport. USB drives, removable hard drives, and physical prints of drawings all qualify.
Screening of individuals with CUI access and ensuring CUI is protected during personnel transfers and terminations.
Restricted physical access, visitor control, maintained visitor logs, secure areas for CUI storage, and alternate work site protection. If someone can walk up to an engineering workstation unchallenged, you fail PE.
Periodic risk assessments, vulnerability scanning, and remediation of identified vulnerabilities.
Periodic security control assessments, plans of action for deficiencies, monitoring of controls on an ongoing basis, and a documented System Security Plan (SSP).
Network segmentation, boundary protection, FIPS 140-2 validated cryptography for CUI at rest and in transit, collaboration device restrictions, and VoIP controls. For manufacturers, this is where GCC High, Azure Government, or a proper CUI enclave usually enters the picture.
Flaw remediation, malicious code protection, system monitoring, and security alert response. Anti-virus alone does not cut it — you need detection and response capability.
Total: 110 requirements, 320 assessment objectives.
This is the part most contractors get wrong, and it matters a lot.
CMMC Level 2 is scored on a point-based system starting at 110. Each unmet control deducts points based on its criticality:
To qualify for conditional Level 2 certification, you need a minimum score of 88 out of 110 (80%). Drop below 88 and you fail — full stop.
This is where defense manufacturers get tripped up most often. CMMC 2.0 allows a Plan of Action and Milestones (POA&M) for some non-critical gaps, giving you 180 days to remediate — but six foundational controls must be fully implemented at the time of assessment.
Under 32 CFR § 170.21, the following security requirements cannot be on a POA&M:
Also barred from POA&M: any control worth 3 or 5 points, with one narrow exception — CUI encryption (SC.L2-3.13.11) can be on a POA&M if encryption is implemented but not yet FIPS-validated.
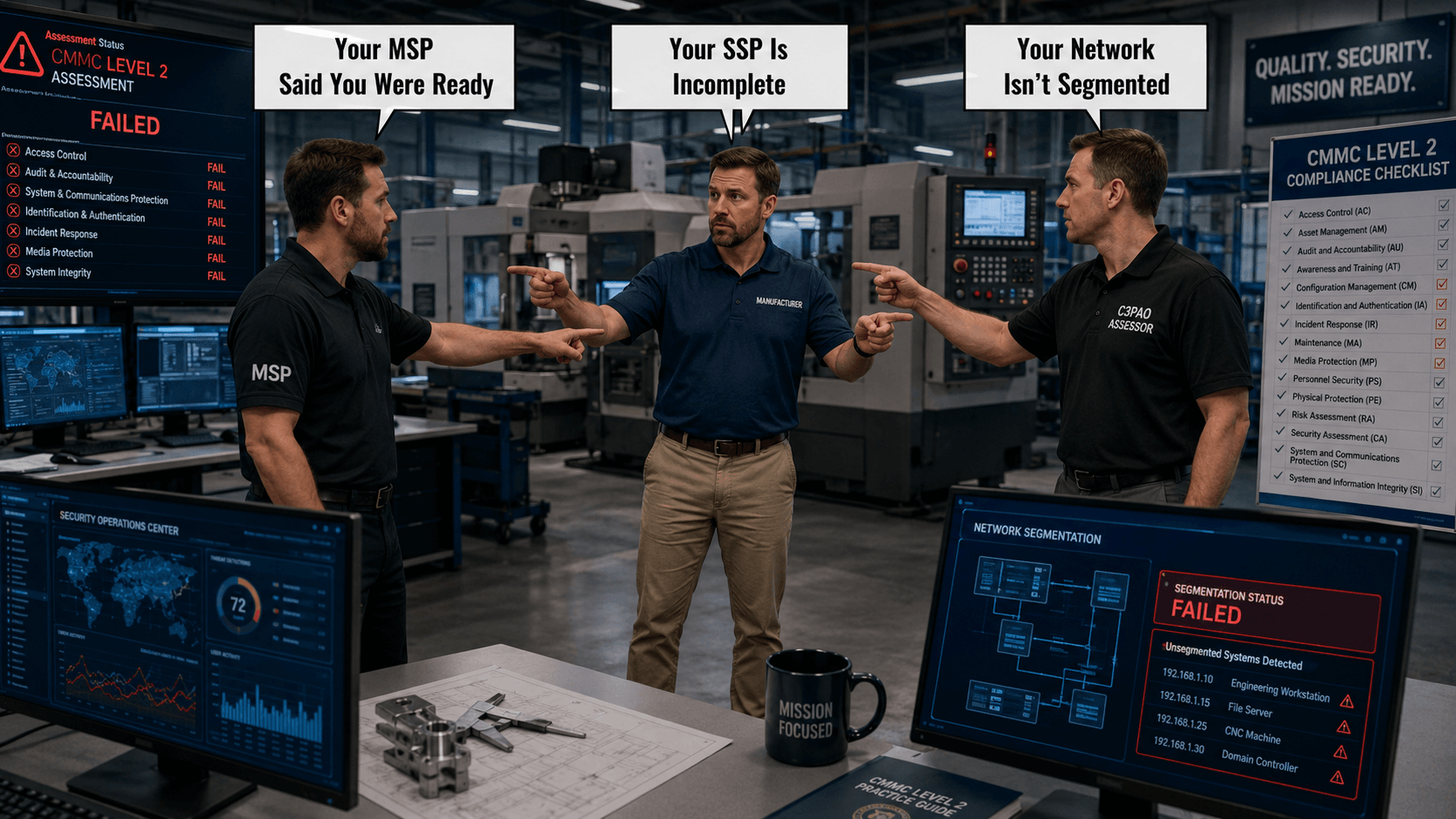
Bottom line: if MFA isn’t in place, if your SSP is missing, or if visitors can walk into your shop floor unchallenged, you will not receive conditional certification. You will fail the assessment and go back to the end of a 9-to-12-month C3PAO queue.
Two outcomes matter:
Conditional Level 2 (C3PAO) — You scored at least 88 out of 110, and all remaining gaps qualify for POA&M inclusion. You have 180 days from the conditional status date to close every POA&M item and pass a formal closeout assessment.
Final Level 2 (C3PAO) — All 110 controls fully implemented and verified. Valid for 3 years. Annual affirmations required.
Miss the 180-day window? Your conditional status expires. You lose certified status. You start over.
The CMMC rollout happens in four phases:
Here is the math defense manufacturers need to run:
A contractor starting today is realistically looking at certification in mid-to-late 2027 — already past the Phase 2 deadline. If you’re not in motion right now, you will miss at least one contract recompete cycle.
Generic CMMC guides treat every environment the same. Real manufacturing shops do not look like law firms or accounting practices. Here is what makes Level 2 harder — and more expensive — for defense manufacturers:
1. Shop-floor OT systems. CNC machines, CMMs, PLC-controlled equipment, and legacy machine controllers often run Windows 7, XP Embedded, or proprietary operating systems that cannot be patched or segmented easily.
2. Engineering file sprawl. Technical drawings and STEP files move between engineering, quoting, CAM programming, inspection, and production. Every stop expands CUI scope.
3. Flat networks. Many machine shops have a single flat LAN where office PCs, CAD workstations, CNC controllers, and quality lab equipment all talk freely. That has to change for CMMC — network segmentation is a major remediation line item.
4. ERP and quoting systems. Epicor, JobBOSS, ProShop, Global Shop, E2, Infor Visual — your ERP almost certainly touches CUI. All of it has to be scoped and documented.
5. Supply chain flow-down. You must flow CMMC requirements to any subcontractor who handles CUI on your behalf. Most shops have no formal mechanism to verify this today.
6. ITAR ≠ CMMC. A common trap. You can be fully ITAR-compliant and still fail CMMC Level 2 because ITAR does not require FIPS-validated encryption, MFA, an SSP, or formal audit logging. CMMC does.
For a typical defense manufacturer, here’s the compressed version of the 12-to-14-month path:
Months 1–2: Scope and Gap
Months 3–6: Remediation
Months 4–7: Documentation (parallel with remediation)
Months 7–9: Pre-Assessment
Months 9–12: C3PAO Assessment
Months 12–18 (if needed): Close out POA&M items within the 180-day window.
From what Capital Cyber sees across the manufacturing DIB every week:
CMMC Level 2 is not a compliance checkbox — it is an operational discipline built around 110 controls, 320 objectives, and 14 families that reshape how a manufacturing business handles information. Do it right, and you protect every DoD dollar on your books for the next decade. Do it wrong, and you lose contract eligibility on the day your current award recompetes.
Defense manufacturers that start their Level 2 journey now — in the first half of 2026 — still have runway. Manufacturers that wait until Q4 2026 are almost guaranteed to miss the Phase 2 deadline.
Ready to take CMMC Level 2 from confusion to a roadmap?
Capital Cyber works exclusively with defense manufacturers, CNC shops, aerospace suppliers, electronics producers, and DoD subcontractors. We build right-sized Level 2 programs that pass C3PAO assessments — no enterprise bloat, no theoretical frameworks, no guesswork.
Book a free CMMC Level 2 Readiness Call with Capital Cyber →
Practical compliance. Real progress. Your path from gap to certification starts with one honest conversation.
Do not wait until you lose a contract to take action. Call (571) 410 3066 or visit capital-cyber.com for a free CMMC readiness consultation.
Capital Cyber | 1019B Edwards Ferry Rd. #1183, Leesburg, VA 20176
Security Obsessed. Service Driven.