Not ready for a Complete Pen Test? How about finding out your Cyber Score in 2 mins? Click here for your Cyber Score
If you manufacture components for Boeing, Lockheed Martin, or any other aerospace prime, you’ve probably gotten “the email” by now.
The one asking about your cybersecurity certification. The one that mentions CMMC. The one that makes you wonder if you’re about to lose your biggest contract.
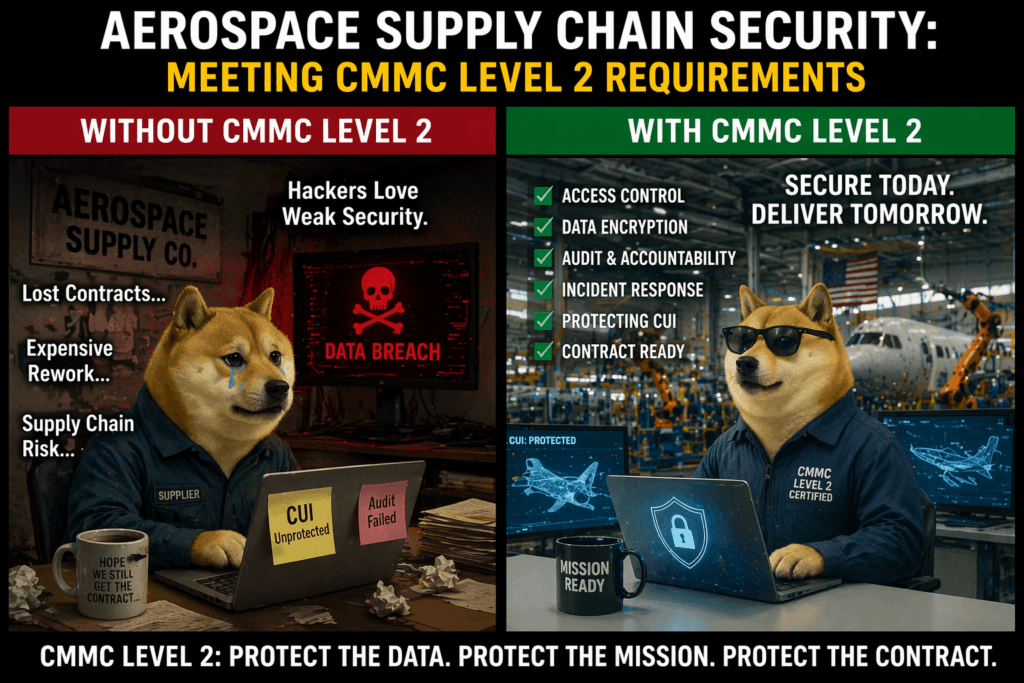
Here’s what’s happening: The aerospace industry is undergoing the biggest security transformation in decades, and CMMC Level 2 isn’t a competitive advantage anymore—it’s the baseline requirement just to stay in the game.
If you’re a Tier 2 or Tier 3 aerospace supplier, this guide will walk you through what CMMC means for your business and how to achieve compliance without derailing operations.
Your company handles some of the most valuable technical data in the world:
Foreign adversaries know this. In the past decade:
Large primes have security operations centers, incident response teams, and million-dollar cybersecurity budgets. You don’t.
Attackers know this. They go after the weakest link: a 50-person sheet metal fabricator or a 20-person avionics shop with shared passwords and unpatched systems.
Real-world example: A Tier 3 landing gear component manufacturer was breached through a phishing email. Attackers stole CAD files for a next-generation fighter jet component. The prime contractor terminated the relationship within 30 days.
If you handle Controlled Unclassified Information (CUI)—which includes almost all technical data from aerospace primes—you need Level 2.
Most suppliers don’t realize how much CUI they actually have:
Rule of Thumb: If it came from a prime contractor and it’s more technical than a purchase order, it’s probably CUI.
Level 2 requires 110 security practices across 14 domains, aligned with NIST SP 800-171. You must:
Here’s what each domain means for aerospace suppliers, with real costs and implementation examples.
What it means: Only authorized people access your systems and data.
For aerospace suppliers:
Common gap: Shared CAD workstation logins, no MFA on engineering systems.
Implementation example: A Tier 2 machinist (30 employees) implemented Azure AD with MFA and role-based groups. Cost: $12,000 setup + $2,400/year.
What it means: Your people know how to handle CUI safely.
For aerospace suppliers:
Common gap: No formal training program or documentation.
Implementation example: A Tier 3 avionics supplier uses KnowBe4 for security awareness. Cost: $3,000/year, 2 hours/person/year.
What it means: Log everything so you can detect and investigate security events.
For aerospace suppliers:
Common gap: Logging disabled, stored locally (easily deleted), never reviewed.
Implementation example: A Tier 2 composite manufacturer deployed Splunk for log aggregation. Cost: $15,000/year for 50 users. Detected credential theft within 48 hours.
What it means: Maintain secure, consistent system configurations.
For aerospace suppliers:
Common gap: No standards, ad-hoc changes, months-old unpatched vulnerabilities.
Implementation example: A Tier 2 sheet metal fabricator uses Microsoft MECM for patch management. Cost: Included with Microsoft 365 E3. Reduced patch time from 6 months to 2 weeks.
What it means: Verify user identities before granting access.
For aerospace suppliers:
Common gap: Shared “admin” or “engineering” accounts, weak passwords, no MFA.
Implementation example: A Tier 3 landing gear manufacturer implemented Duo Security for MFA. Cost: $3/user/month. Prevented 17 phishing-based account compromises in year one.
What it means: Detect, respond to, and recover from cyberattacks.
For aerospace suppliers:
Common gap: No plan, no idea who to call, never tested.
Implementation example: A Tier 2 electronics manufacturer hired a vCSO to develop IR plan and conduct tabletop exercises. Cost: $24,000/year retainer.
What it means: Perform maintenance while maintaining security.
For aerospace suppliers:
Common gap: Vendor techs connect unsupervised, USB drives used without scanning, remote access left open 24/7.
Implementation example: A Tier 2 aerospace machining company requires all vendor maintenance through company-provided laptops via VPN with MFA. Cost: $10,000 for procedures and equipment.
What it means: Protect CUI on physical and digital media.
For aerospace suppliers:
Common gap: Unmarked USB drives with CUI, old PCs donated without wiping, drawings in trash.
Implementation example: A Tier 3 fastener manufacturer uses encrypted USBs only ($80 each), shreds all CUI paper ($2,000 shredder), contracts certified e-waste vendor ($500/year). Total: $5,000 setup + $500/year.
What it means: Screen people who access CUI.
For aerospace suppliers:
Common gap: No background checks, checks not documented, delayed access revocation.
Implementation example: A Tier 2 supplier uses Accurate Background ($50/check) for all employees with CUI access before hire and every 5 years. Cost: $2,500/year for 50 employees.
What it means: Limit physical access to systems and CUI areas.
For aerospace suppliers:
Common gap: Open access to engineering offices, no visitor log, servers in unlocked closets.
Implementation example: A Tier 2 composite parts manufacturer installed badge access for engineering areas ($15,000), 8 security cameras ($8,000), visitor sign-in ($0), locked server room with UPS ($5,000). Total: $28,000.
What it means: Identify and manage cybersecurity risks.
For aerospace suppliers:
Common gap: Never performed risk assessment, no vulnerability scanning, known issues not tracked.
Implementation example: A Tier 3 precision parts manufacturer uses Tenable Nessus for scanning ($2,400/year) and hires consultant for annual risk assessment ($8,000/year). Total: $10,400/year.
What it means: Test and evaluate security controls.
For aerospace suppliers:
Common gap: No formal assessment, security never tested, assume “it’s working.”
Implementation example: A Tier 2 avionics supplier conducts annual internal assessments (2 days, internal IT) and engages third-party consultant every 2 years ($15,000). Cost: ~$8,000/year averaged.
What it means: Monitor, control, and protect communications and systems.
For aerospace suppliers:
Common gap: No firewall or misconfigured, CUI sent via unencrypted email, no encryption on laptops, guest Wi-Fi on same network.
Implementation example: A Tier 2 sheet metal fabricator deployed Palo Alto firewall with IDS/IPS ($15,000 + $3,000/year), enabled BitLocker ($0), segmented network with VLANs ($5,000), deployed VPN with MFA ($10,000 + $5,000/year). Total: $30,000 setup + $8,000/year.
What it means: Identify, report, and correct system flaws.
For aerospace suppliers:
Common gap: No antivirus or outdated, patches months behind, no email filtering, nobody monitors alerts.
Implementation example: A Tier 3 machining company deployed Microsoft Defender for Endpoint ($57/user/month with M365 E5), Proofpoint for email security ($8/user/month), automated patch management via MECM (included). Total: $65/user/month (~$39,000/year for 50 employees).
Prime contractors are requiring CMMC NOW. Boeing, Lockheed Martin, Northrop Grumman, and Raytheon are demanding certifications from suppliers before awarding new contracts.
Quote from Leidos CISO:
“They can’t just pick the best solution or best partner because of margin or capacity. Now they have to bring forward this representation of compliance—that’s what the government is asking us to do as primes.”
Bottom line: If you’re not working on CMMC now, you’re already behind.
Year 1:
Years 2-3:
Year 4 (Re-assessment):
3-year investment: $255K-$520K
Typical Tier 2 aerospace supplier:
ROI: If CMMC protects just ONE contract, your ROI is 3,000%-20,000%.
Month 3 (Quick Wins):
Month 4 (Infrastructure):
Month 5 (Advanced Controls):
Quality certifications don’t address cybersecurity. CMMC is a completely different framework.
Assessors test controls in real-time. They’ll try to log in without MFA, verify encryption is enabled, check if logs are reviewed, test incident response.
Paper documentation isn’t enough.
By the time your customer demands CMMC, you’re 6-12 months away. You’ll lose the contract.
Your IT person (even if skilled) likely doesn’t have CMMC expertise. Hire help.
Your suppliers need CMMC too if they touch CUI. This includes engineering firms, CAD/PLM vendors, cloud providers, IT service providers.
You’re responsible for their gaps.
1. Identify DoD contracts involving CUI
2. Talk to your primes about their timeline
3. Review current security (MFA? Encryption? Backups?)
1. Get a gap assessment (hire consultant or use free tools)
2. Calculate budget and ROI
3. Build compliance timeline
1. Hire CMMC consultant or MSSP
2. Start quick wins (MFA, encryption, training)
3. Begin System Security Plan documentation
CMMC Level 2 is achievable for aerospace suppliers of all sizes. The key is starting early, investing wisely, and treating cybersecurity as a business enabler—not just a compliance checkbox.
The aerospace supply chain is consolidating. Companies with CMMC certification will thrive. Those without will be left behind.
Your next steps:
1. This week: Preliminary self-assessment
2. This month: Engage CMMC consultant or MSSP
3. This quarter: Complete gap analysis and begin remediation
4. Within 6 months: Schedule C3PAO assessment
The time to act is now.
—
Capital Cyber specializes in CMMC compliance for aerospace and defense manufacturers. We’ve helped dozens of Tier 2 and Tier 3 suppliers achieve Level 2 certification on time and on budget.
What we do: