Not ready for a Complete Pen Test? How about finding out your Cyber Score in 2 mins? Click here for your Cyber Score
Published by Capital Cyber | Leesburg, VA | (571) 410 3066
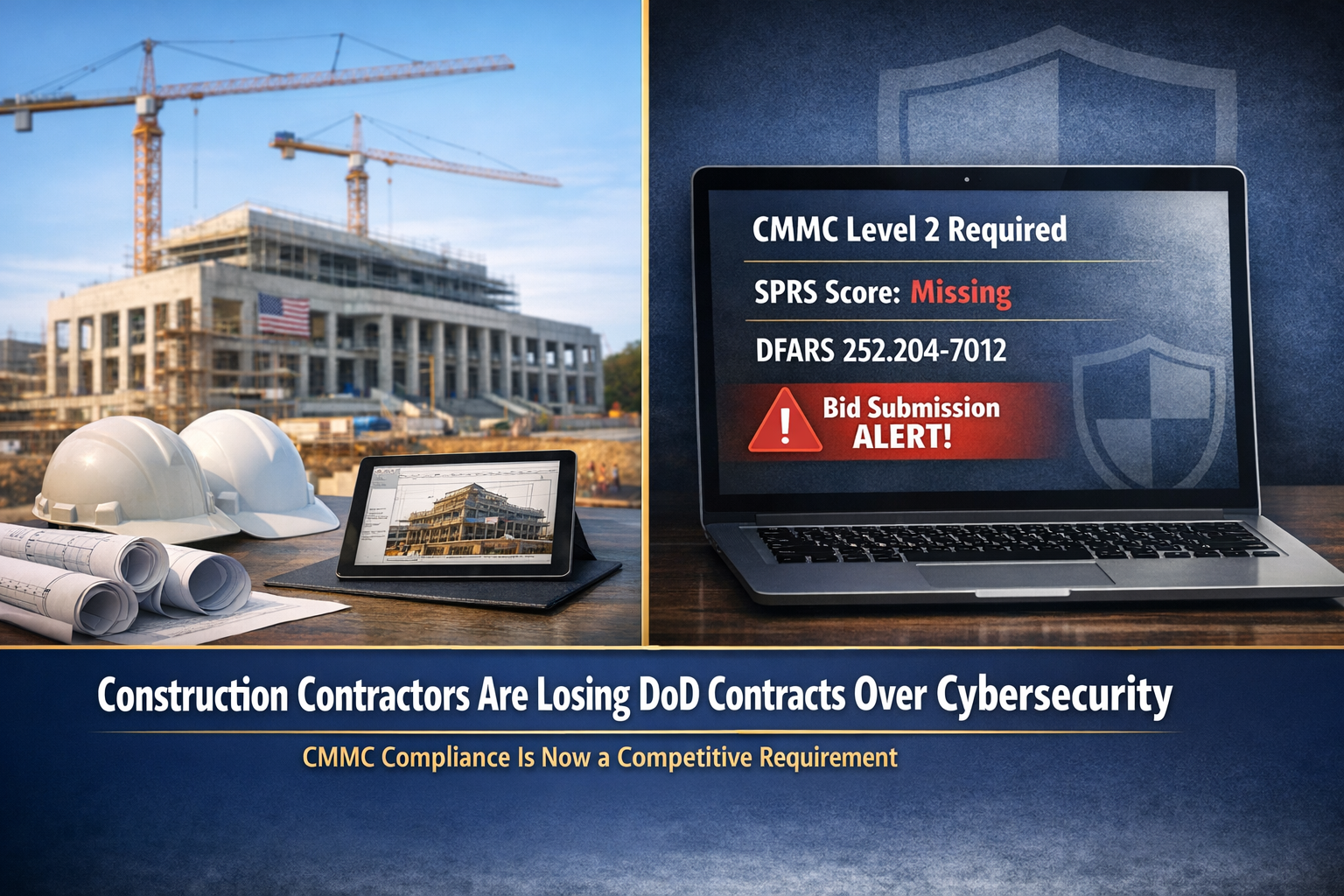
The construction industry is facing a cybersecurity reckoning, and most contractors do not see it coming.
While manufacturers and IT companies have been preparing for CMMC for years, the construction sector has largely operated under the assumption that cybersecurity requirements “don’t really apply to us.” That assumption is now costing contractors real money on real projects.
DoD construction contracts are being awarded to competitors who can demonstrate cybersecurity compliance. Primes are dropping subcontractors who cannot prove they protect Controlled Unclassified Information. And the contractors who wait until a contracting officer asks about their CMMC status will be too late.
This is not a theoretical future risk. It is happening now.
Construction contractors are reporting that they are losing competitive bids not because of pricing, qualifications, or past performance, but because they cannot demonstrate compliance with DFARS cybersecurity clauses. Contracting officers now routinely check SPRS scores and cybersecurity self assessments as part of the evaluation process.
A contractor who submits the lowest bid but has no SPRS score on file, or worse, has an inaccurate score, faces disqualification before their technical proposal is even reviewed.
General contractors on DoD projects are required under DFARS 252.204 7012 to flow down cybersecurity requirements to subcontractors who handle CUI. As primes face increasing pressure to demonstrate their own CMMC compliance, they are taking a hard look at their subcontractor base.
Subcontractors who cannot provide evidence of cybersecurity compliance are being replaced. The relationships you have built over decades of quality work can be undone by an inability to answer basic questions about how you protect digital project data.
Here is a risk that keeps compliance attorneys up at night: the False Claims Act. When a contractor submits a bid that includes a representation of DFARS compliance (as most DoD construction contracts require), that representation becomes a legal statement to the federal government. If your actual cybersecurity posture does not match your representation, you are potentially liable for false claims.
False Claims Act penalties include treble damages and per claim penalties. For construction contractors with multiple DoD contracts, the financial exposure can be devastating. The Department of Justice has publicly stated that cybersecurity fraud is an enforcement priority.
The Defense Contract Management Agency’s Defense Industrial Base Cybersecurity Assessment Center (DIBCAC) conducts audits of defense contractors’ cybersecurity self assessments. If DIBCAC audits your self assessment and finds that your actual implementation falls far short of your reported SPRS score, the consequences range from mandatory remediation plans to contract termination.
Construction contractors have historically received less DIBCAC attention than manufacturers, but that is changing as the DoD broadens its audit scope across the entire defense industrial base.
The biggest vulnerability in construction cybersecurity is not a technical gap. It is a cultural one. Construction companies have operated for generations on the assumption that cybersecurity is an IT problem, and most construction companies barely have IT departments, let alone security programs.
This mindset creates blind spots. Project managers sharing building plans via unencrypted email. Superintendents accessing controlled drawings on personal phones. Estimators storing sensitive bid data on unprotected laptops. Office managers using the same password across every system.
Each of these everyday practices represents a CMMC violation and a genuine security risk.
Construction contractors working on DoD facilities handle information that adversaries actively target. Building plans for military installations reveal force protection measures, physical security layouts, utility infrastructure, and structural vulnerabilities. HVAC and mechanical drawings show how secure spaces are configured. Electrical plans reveal communication infrastructure.
This information is classified as CUI specifically because it would be valuable to adversaries seeking to target military installations. Treating it casually is not just a compliance problem. It is a national security problem.
On a typical DoD construction project, the general contractor might share project data with 20 to 50 subcontractors. Each subcontractor becomes a potential vulnerability in the information supply chain. Mechanical, electrical, plumbing, fire protection, structural steel, concrete, roofing, and dozens of specialty contractors all receive portions of the project data.
If even one subcontractor stores CUI on an unsecured system, the entire project’s information security is compromised. And under DFARS flow down requirements, the prime contractor bears responsibility for ensuring subcontractor compliance.
Construction companies operate across multiple temporary jobsites with improvised IT infrastructure. Project trailers with consumer grade networking equipment. Field offices with shared workstations. Superintendents using mobile hotspots. These temporary environments are inherently more difficult to secure than permanent office installations, yet they frequently handle CUI.
The Associated General Contractors of America (AGC) and other construction industry organizations have been sounding the alarm about CMMC’s impact on construction contractors. Industry associations have warned that many construction companies are unprepared for the cybersecurity requirements that are now being included in DoD solicitations.
The message from industry leaders is consistent: construction contractors need to treat CMMC compliance with the same seriousness they treat safety compliance, bonding requirements, and quality certifications. It is becoming a fundamental cost of doing business in the federal construction market.
Review your current DoD contracts and any solicitations you plan to bid. Look for DFARS clauses 252.204 7012, 7019, and 7020. If you handle CUI (building plans, security specifications, infrastructure details for DoD facilities), you almost certainly need CMMC Level 2.
Do you have a firewall? Multi factor authentication? Encrypted email? Access controls on project data? An incident response plan? Backup and recovery procedures? Security awareness training? If you answered “no” or “I’m not sure” to any of these, you have significant gaps to close.
If you submitted an SPRS score that does not accurately reflect your security posture, you need to correct it. Yes, a corrected score may be lower, but an accurate low score is infinitely better than an inaccurate high score when DIBCAC comes calling.
Generic IT companies do not understand construction operations. You need a cybersecurity partner who understands project based IT environments, multi site security challenges, subcontractor management, and the practical realities of an industry that works in the field, not in cubicles.
Capital Cyber works with construction contractors across the mid Atlantic region to achieve CMMC compliance with solutions designed for how construction companies actually operate.
CMMC Level 2 certification requires 12 to 18 months of preparation. If you are bidding on DoD contracts in 2026 that include CMMC requirements, the window for starting preparation is closing. Every month you delay adds risk to your contract pipeline.
CMMC compliance is not something to delegate to the office manager or the part time IT contractor. It requires executive commitment, budget allocation, and organizational buy in. The construction companies that treat cybersecurity as a strategic business requirement will win contracts. Those that treat it as a nuisance will lose them.
Here is the upside that most construction contractors miss: CMMC compliance is a competitive differentiator. Right now, the majority of construction contractors in the DoD market are not CMMC certified. The contractors who achieve certification first will have a significant competitive advantage.
When a contracting officer evaluates two qualified bidders and one is CMMC certified while the other is not, the certified contractor wins. When a prime contractor needs a subcontractor for a DoD project and one can demonstrate compliance while others cannot, the compliant sub gets the call.
The contractors who invest in compliance now are not just protecting existing revenue. They are positioning themselves to capture market share from competitors who failed to prepare.
Capital Cyber is a cybersecurity firm in Leesburg, VA with 24 years of IT and cybersecurity experience. We help construction contractors achieve CMMC compliance with practical solutions designed for project based businesses.
Our services for construction contractors include:
Do not wait until you lose a contract to take action. Call (571) 410 3066 or visit capital-cyber.com for a free CMMC readiness consultation.
Capital Cyber | 1019B Edwards Ferry Rd. #1183, Leesburg, VA 20176
Security Obsessed. Service Driven.