CMMC vs. ITAR: What Defense Manufacturers Need to Understand
Published by Capital Cyber | Leesburg, VA | (571) 410 3066
If you own or manage a machine shop that does defense work, you have probably been hearing about CMMC for years now. The acronyms keep piling up. The deadlines keep shifting. And the advice you get ranges from “it is no big deal” to “you need to spend $500,000 immediately.”
Here is the truth: CMMC Level 2 is real, it is happening in 2026, and it will determine whether your shop keeps its DoD contracts. But it is also manageable if you understand what is actually required and take a practical approach.
This guide cuts through the noise and tells you what a small to mid size machine shop actually needs to know about CMMC Level 2 in 2026.
What CMMC Level 2 Actually Requires
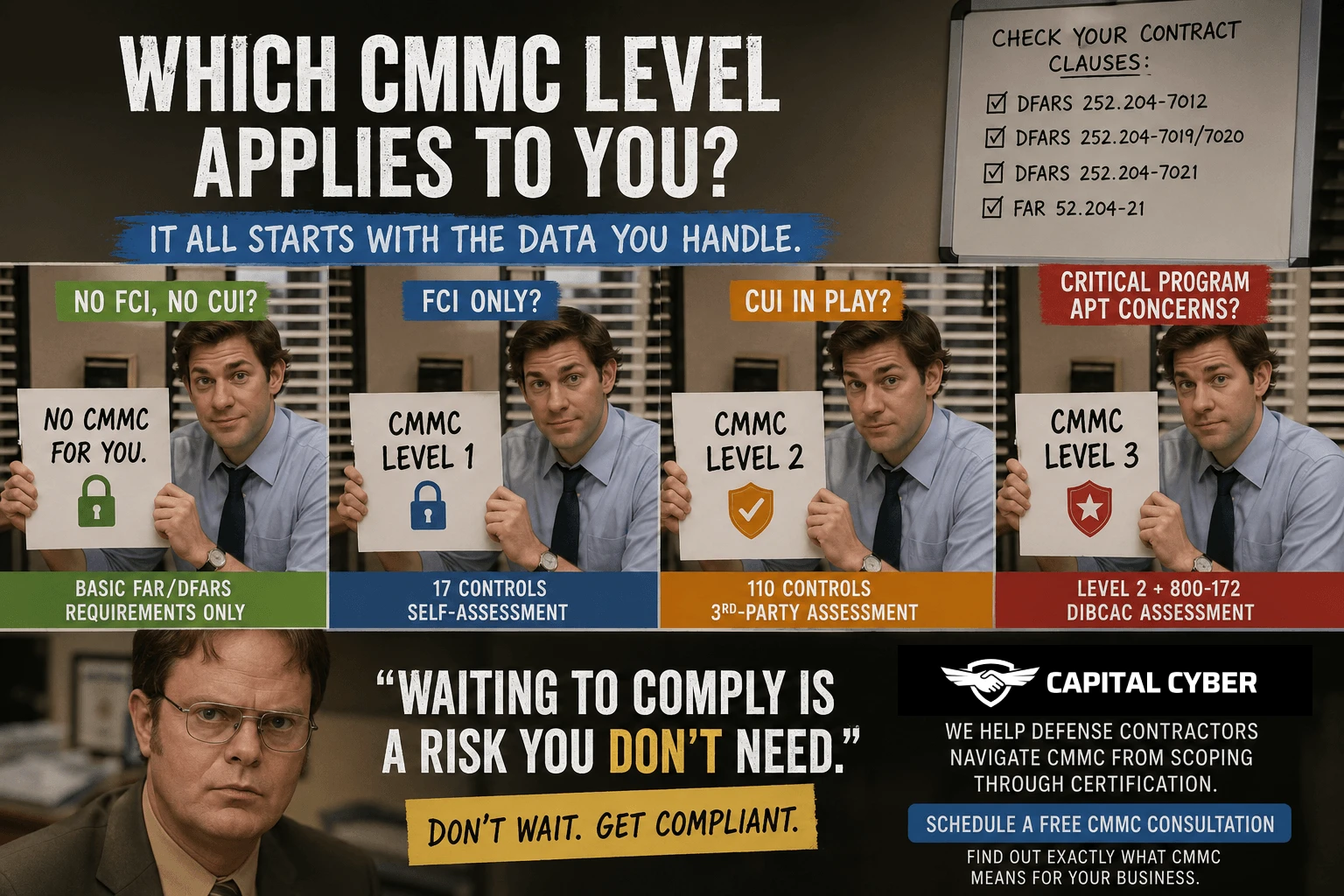
CMMC Level 2 is based on 110 security controls from NIST SP 800 171 Revision 2. These controls cover 14 areas including access control, audit logging, configuration management, incident response, and more.
If your machine shop handles Controlled Unclassified Information (CUI), which includes technical drawings, specifications, tolerances, material callouts, process instructions, and test data from DoD contracts, you need Level 2.
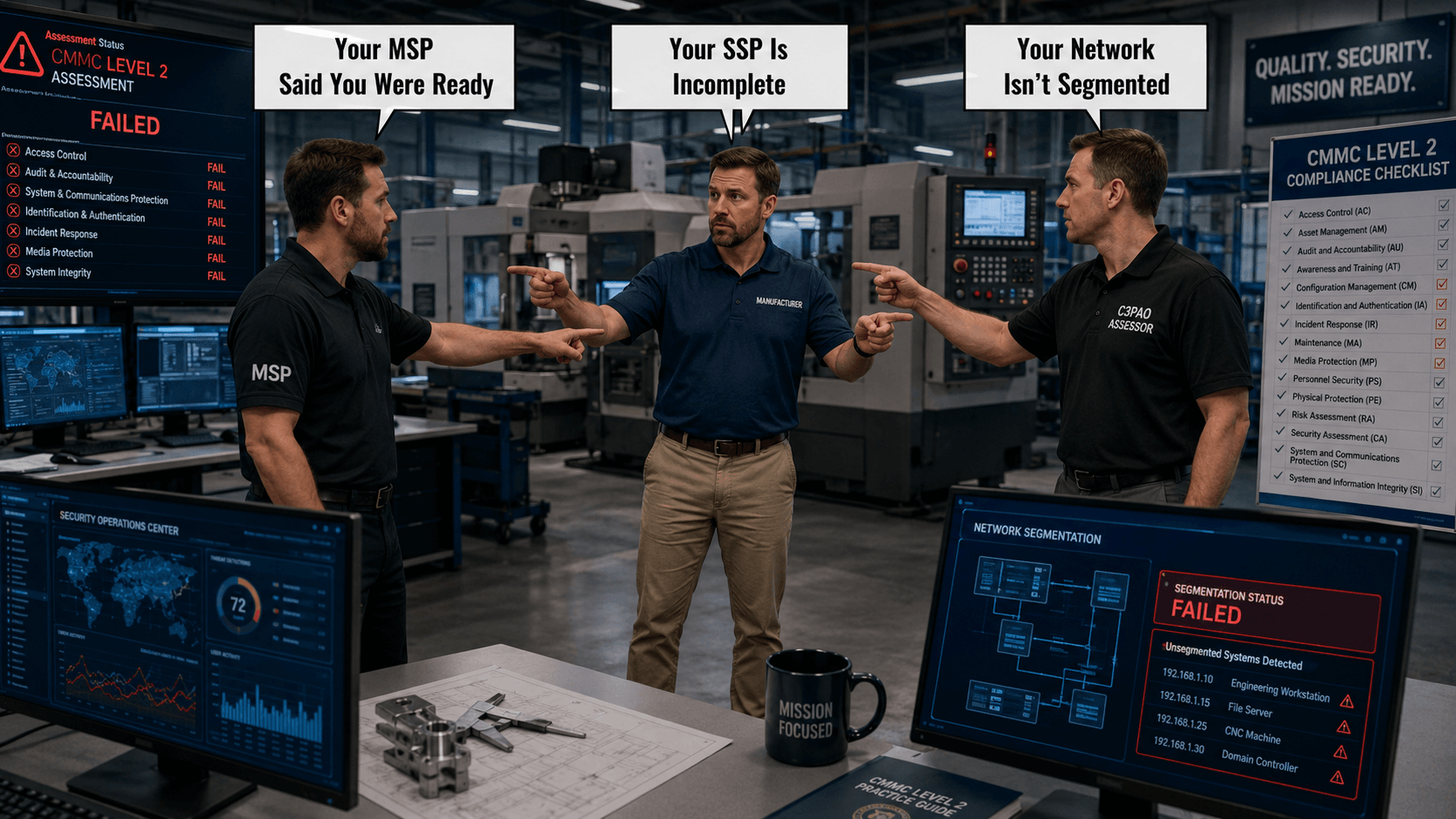
Level 2 requires a third party assessment by an authorized C3PAO (CMMC Third Party Assessor Organization). This is not a self assessment. An independent team will come to your facility, review your documentation, interview your people, and test your systems.
The 110 controls are not optional. You must demonstrate that each applicable control is implemented, documented, and operational. Partial implementation does not count.
The Legacy Equipment Problem
Here is where machine shops face a challenge that most cybersecurity consultants do not understand: your shop floor is full of equipment that was never designed with cybersecurity in mind.
That Fanuc controller running your CNC mill? It is probably running an embedded operating system from 2005. Your Haas machines might connect to your network for program transfers but offer zero security features. Your wire EDM might use a Windows XP based controller that has not seen a security patch in over a decade.
These machines cost hundreds of thousands of dollars. You cannot replace them for compliance. You cannot install antivirus on a CNC controller. And you certainly cannot take them offline for security updates during a production run.
The good news: CMMC does not require you to install endpoint protection on every CNC controller. But it does require you to address the risk these systems create. Here is how.
Network Segmentation
The most effective approach for legacy shop floor equipment is network segmentation. Your CNC machines, PLCs, and other industrial control systems should be on a separate network segment (often called an OT or operational technology network) that is isolated from your IT network where CUI is processed.
This means your Fanuc controller can still receive programs over the network, but it cannot reach your file server, your email system, or your ERP database. If an attacker compromises a legacy machine, they hit a dead end instead of gaining access to your sensitive data.
Compensating Controls
For legacy systems that must interact with CUI (for example, a CNC machine that receives programs containing controlled technical data), compensating controls become essential. These might include dedicated transfer stations that scan files before loading them onto machines, monitoring solutions that detect anomalous network traffic from shop floor equipment, physical access controls that restrict who can interact with machine controllers, and logging mechanisms that track program transfers and modifications.
The Enclave Approach: Your Best Friend
Here is the strategy that saves most machine shops significant money and complexity: the enclave approach.
Instead of securing your entire network, every computer, every device, and every system to CMMC Level 2 standards, you create a defined enclave where CUI is processed, stored, and transmitted. Everything inside the enclave meets all 110 controls. Everything outside the enclave operates under your normal security practices.
For a typical machine shop, the enclave might include a secure file server for technical data packages, workstations used by engineers and programmers who access CUI, the email system (or a dedicated email system) used for CUI communications, and backup systems that contain copies of CUI.
The enclave does NOT need to include general office computers used for accounting and HR, shop floor CNC machines (if properly segmented), personal devices, or systems that never touch CUI.
By limiting your CMMC boundary to a well defined enclave, you can reduce your assessment scope by 50% to 80%, dramatically lowering both preparation costs and ongoing compliance burden.
Capital Cyber specializes in designing enclaves for manufacturing environments that keep engineers and machinists productive while maintaining full CMMC compliance.
The Real Cost for a Machine Shop
Let us talk numbers honestly. The internet is full of wildly varying cost estimates for CMMC Level 2. Here is what a small to mid size machine shop (10 to 75 employees) should realistically budget:
Gap Assessment and Scoping: $5,000 to $15,000
This is where you find out where you actually stand. A proper gap assessment evaluates your current security posture against all 110 controls and tells you exactly what needs to change.
Remediation and Implementation: $30,000 to $100,000+
This is the biggest variable. If you already have decent IT infrastructure and some security practices in place, remediation costs less. If you are starting from a shared password and no firewall situation, costs go up. This includes security tools, system upgrades, network reconfiguration, and the labor to implement everything.
Documentation: $10,000 to $25,000
Your System Security Plan, policies, procedures, incident response plan, and supporting documentation. This is often underestimated. Assessors spend significant time reviewing documentation, and generic templates do not pass muster.
C3PAO Assessment: $25,000 to $75,000
The actual third party assessment fee. This varies by C3PAO and the size/complexity of your environment.
Ongoing Annual Costs: $15,000 to $50,000
Security tools, monitoring, annual affirmation, employee training, and maintaining compliance between triennial assessments.
Total First Year: $50,000 to $150,000+
Is that a significant investment for a small machine shop? Yes. But consider the alternative: losing your DoD contracts entirely. For most defense machine shops, DoD work represents 30% to 80% of revenue. The cost of compliance is a fraction of the cost of losing that work.
Capital Cyber’s Audit Ready package is designed specifically for this scenario, providing everything from gap assessment through assessment preparation in a structured, predictable engagement.
The Timeline You Need to Follow
If you have not started CMMC preparation and you need Level 2 certification, here is a realistic timeline:
Months 1 to 2: Scoping and Gap Assessment
Determine what CUI you handle, where it lives, how it flows, and what your current security gaps are. This is the foundation of everything that follows.
Months 3 to 4: Remediation Planning
Create your Plan of Action and Milestones (POA&M) and design your enclave architecture. This is where you make the key decisions about your CMMC boundary, your technology stack, and your implementation sequence.
Months 5 to 12: Implementation
Close your gaps. Deploy security tools. Implement access controls, multi factor authentication, encryption, logging, and monitoring. Build your documentation. Train your people. This is the longest phase and the most work.
Months 13 to 14: Assessment Preparation
Conduct mock assessments, collect evidence, prepare personnel for interviews, and verify that everything works as documented.
Month 15 to 16: C3PAO Assessment
Schedule and complete your official assessment.
That is roughly 16 months from start to certification. If your contracts start requiring CMMC certification in mid to late 2026, you need to be starting now.
Your First Steps: What to Do This Month
If you are a machine shop owner reading this and feeling overwhelmed, here are five concrete actions you can take right now:
- Identify Your CUI
Pull your DoD contracts and look at the DFARS clauses. If you see 252.204 7012, you handle CUI and need Level 2. Make a list of every type of CUI you receive, create, process, and transmit.
- Map Your Data Flow
Trace how CUI moves through your shop. Where does it come in? (Email? Secure portal? Physical media?) Where does it go? (CNC machines? Engineers’ workstations? Subcontractors?) Where is it stored? (File server? Cloud? USB drives?)
- Check Your SPRS Score
If you submitted an SPRS score, is it accurate? If your score does not reflect your actual implementation, you have a problem that needs to be addressed. An inaccurate SPRS score creates legal liability under the False Claims Act.
- Assess Your Network
Do you know what is on your network? Can you draw a network diagram that shows every device, every connection, and every path between your office systems and your shop floor? If not, you need a network assessment.
- Call Capital Cyber
Seriously. A free initial consultation with a cybersecurity firm that understands manufacturing will give you clarity on where you stand and what you need to do. We have helped machine shops across Virginia and the mid Atlantic region navigate CMMC compliance, and we can help you build a realistic plan that fits your budget and timeline.
Call (571) 410 3066 or visit capital-cyber.com to get started.
Capital Cyber | 1019B Edwards Ferry Rd. #1183, Leesburg, VA 20176
A cybersecurity firm providing IT, not an IT company providing cybersecurity.


![CMMC Level 1 Requirements for Small DoD Contractors [2026]](https://capital-cyber.com/wp-content/uploads/2026/04/cmmc-level-1-requirements-small-dod-contractors-2026.png)
Leave feedback about this